Anthropic Leaked Claude Code
A 59.8 MB debug file shipped with Claude Code v2.1.88. Inside: 512K lines of TypeScript, an unreleased model roadmap, and a Tamagotchi.

On March 31, 2026, Anthropic shipped Claude Code v2.1.88 with a 59.8 MB source map that reconstructed the tool's entire client-side codebase. The file exposed roughly 512,000 lines of TypeScript, an unreleased model roadmap, a hidden Tamagotchi, and a stealth mode for Anthropic employees. This post breaks down what was inside and why it matters.
TL;DR A forgotten
.mapfile in the npm package let anyone reconstruct 512K lines of Claude Code's TypeScript source. Inside: a 6-layer permission stack, an unshipped always-on agent (KAIROS), a Tamagotchi pet system (BUDDY), an undercover mode that strips AI attribution from commits, anti-distillation traps, and internal model codenames mapping to unreleased versions above Opus.
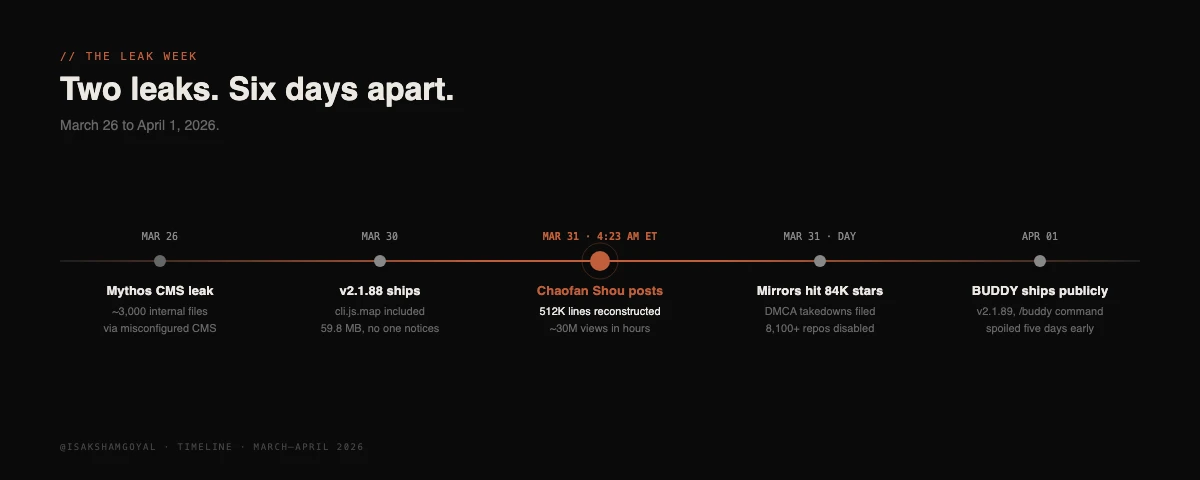 Timeline of the Claude Code source leak from March 26 to April 1, 2026
Timeline of the Claude Code source leak from March 26 to April 1, 2026
The discovery
4:23 AM ET, March 31. Security researcher Chaofan Shou (@Fried_rice, Solayer Labs intern) posted on X that the latest Claude Code npm package was shipping with a source map. He attached a download link.
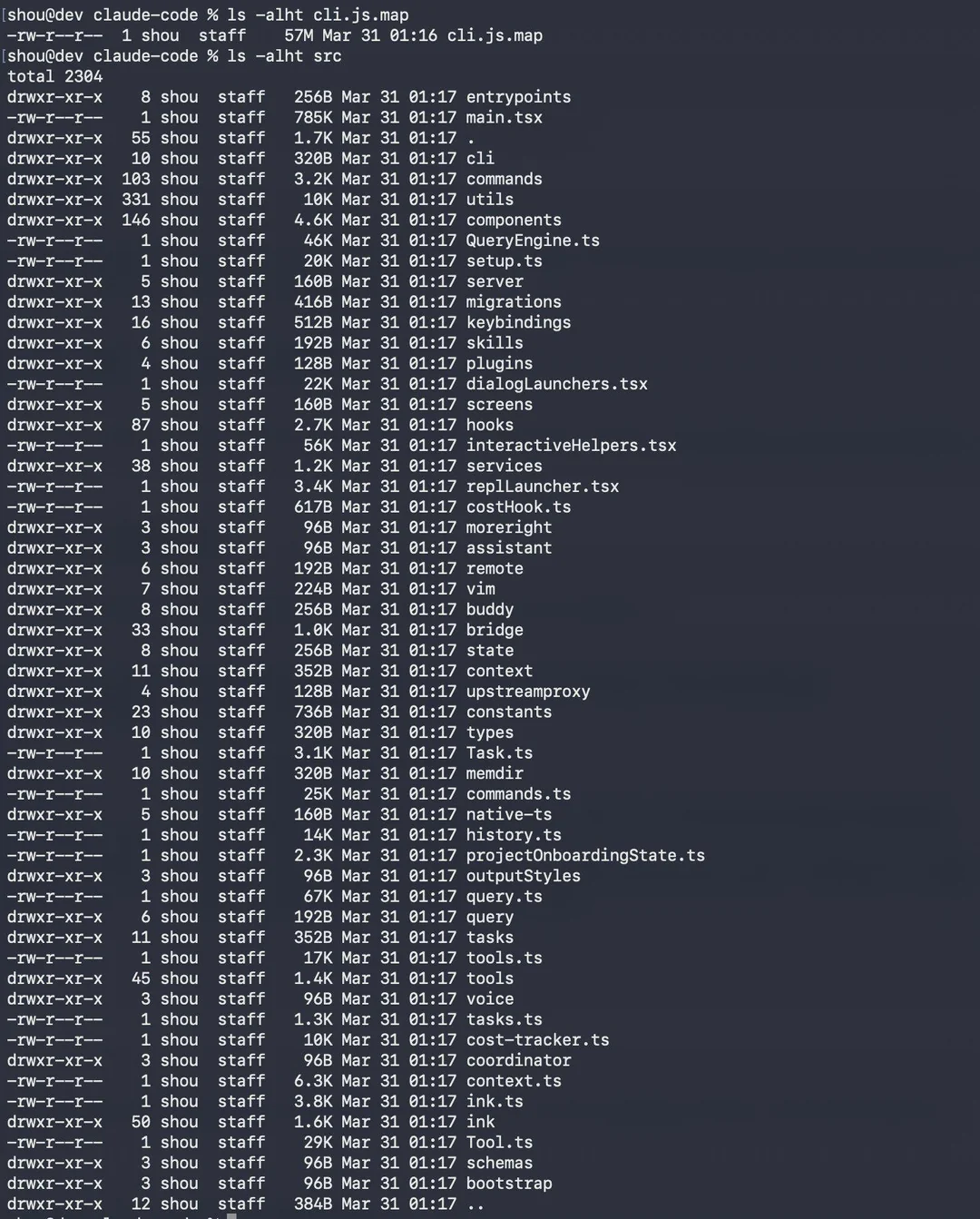 Claude Code's leaked file tree, captured from the public mirror that appeared within hours of the source map being spotted on npm. (Source: @Fried_rice on X)
Claude Code's leaked file tree, captured from the public mirror that appeared within hours of the source map being spotted on npm. (Source: @Fried_rice on X)
The post crossed 16 million views in hours. Mirrors hit 84,000 stars and 82,000 forks before DMCA takedowns landed. GitHub eventually disabled over 8,100 related repos.
How one forgotten file caused this
Source maps exist to bridge minified production code back to readable source for debugging. They are not supposed to ship publicly.
Claude Code uses Bun as its build runtime. Bun generates source maps by default. To prevent them from publishing, the team needed to add *.map to .npmignore. Nobody did.
Boris Cherny, head of Claude Code, called it a "plain developer error." Anthropic's official line: "release packaging issue caused by human error, not a security breach." No customer data, conversation history, or model weights were exposed.
A few details that compound the embarrassment:
- This was reportedly at least the second time in 13 months.
- The Bun source map default behavior had a known bug filed 20 days earlier.
- Anthropic owns Bun as of late 2025.
- The takedown was slow. The npm package was first marked
deprecatedrather than fully unpublished.
Five days earlier, on March 26, a separate CMS misconfig had exposed roughly 3,000 internal files including draft posts about an unannounced model called Mythos. Two leaks in one week, at the company whose entire brand is built on safety-first engineering.
What was inside
The reconstructed codebase totaled approximately 512,000 lines of TypeScript across 1,906 files.
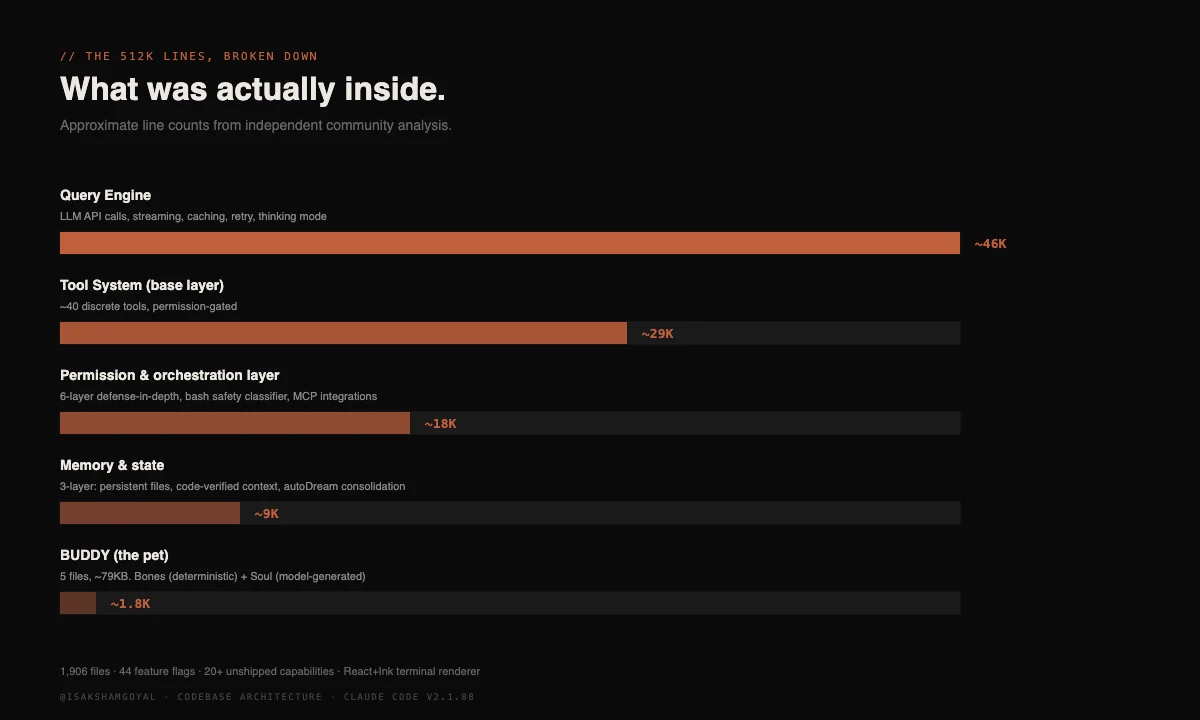 Codebase architecture breakdown by approximate lines of code
Codebase architecture breakdown by approximate lines of code
Reviewers across Hacker News and DEV Community described Claude Code as closer to a small operating system for software engineering than a chat wrapper around an API. Highlights from the architectural breakdown:
- Multi-agent orchestration that fits inside a single system prompt.
- 6-layer permission and safety stack, including a bash command classifier.
- 3-layer memory system, with persistent files, code-verified context, and idle-time consolidation.
- 44 feature flags, roughly 20 of them gating features that have not been publicly announced.
- React + Ink rendering the entire terminal UI.
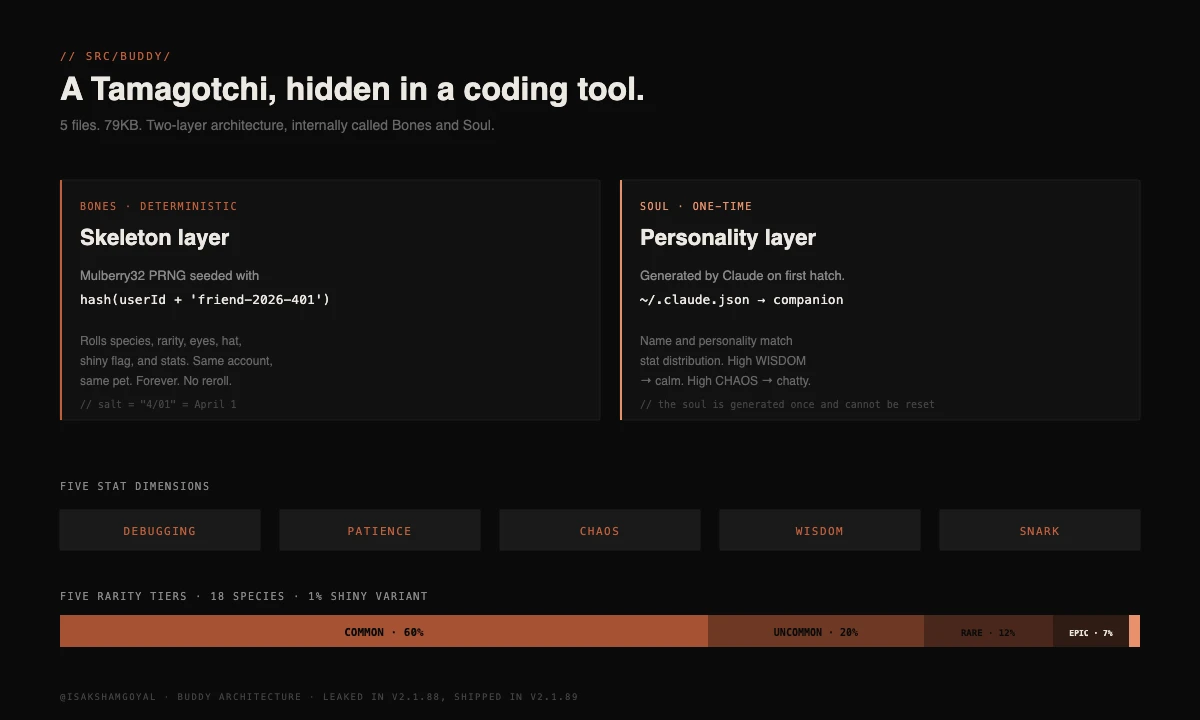
BUDDY: the hidden pet
A fully-realized Tamagotchi-style virtual pet, hidden in src/buddy/.
 BUDDY system architecture
BUDDY system architecture
The system spans 18 species across 5 rarity tiers (60% Common, 1% Legendary), with five stat dimensions: DEBUGGING, PATIENCE, CHAOS, WISDOM, and SNARK.
Two layers, internally named:
- Bones. Deterministic. A Mulberry32 PRNG seeded with
hash(userId + 'friend-2026-401')rolls species, rarity, eyes, hat, shiny flag, and stats. Same account, same pet. Forever. - Soul. Generated by Claude on first hatch and stored in
~/.claude.json. The personality matches the stat distribution. High WISDOM gets a calm pet. High CHAOS gets a chatty one.
The salt string friend-2026-401 is not random. It encodes April 1. Source comments described a teaser window of April 1-7 and a planned full launch in May. The /buddy command did activate on April 1 in v2.1.89 with a Pro subscription requirement. The leak spoiled the surprise by one day.
Most quoted source comment from this directory: "Buddy is a separate entity and is not you (Claude)."
KAIROS: the always-on agent
Referenced over 150 times in the leaked source. Named after the Greek concept of "the right moment." KAIROS is an unshipped autonomous daemon mode.
- Persistent across sessions. It does not stop when you close the terminal.
- Periodic tick prompts. A
<tick>runs on a schedule and decides independently whether to act. - GitHub webhook subscriber. Listens to repo events without a user-initiated request.
- autoDream consolidation. While you are idle, a forked subagent merges observations, removes contradictions, and tightens memory state. Read-only bash access.
- ULTRAPLAN. Companion feature that offloads complex planning to a remote Opus 4.6 session with up to 30 minutes of think time.
KAIROS, like roughly 20 other features behind feature flags, compiles to false in external builds. It exists in the codebase but is inert for current public users.
Undercover mode
The most heated debate in the leak.
 The actual Undercover Mode system prompt
The actual Undercover Mode system prompt
The mode strips three things from generated commits, PRs, and code comments:
- The
Co-Authored-ByAI attribution. - References to internal Anthropic projects, Slack channels, or system specifics.
- Mentions of unreleased model codenames (Capybara, Tengu) or version numbers like
opus-4-7andsonnet-4-8.
In external builds, the entire module is dead-code-eliminated. It has no effect on outside developers using Claude Code on their own projects.
Two reads. Defenders argue the file is largely about preventing accidental disclosure of internal codenames, which is a normal corporate concern. Critics quoted on Hacker News: "if a tool is willing to conceal its own identity in commits, what else is it willing to conceal?"
Anti-distillation and the frustration regex
Two smaller findings drew sharp attention.
- Anti-distillation injection. A flag named
ANTI_DISTILLATION_CCinjectsanti_distillation: ['fake_tools']into outgoing API requests. Decoy tool definitions log alongside real ones. If a competitor scrapes the traffic to train on it, they train on the decoys too. Reviewers noted the mechanism is trivially defeated by a proxy stripping the field. - Frustration tracking. An extensive regex matches swear words and negative-sentiment phrases in user prompts. Telemetry feeds Datadog alongside counters for repeated
continueprompts. Hacker News mocked it as "the world's most expensive company using regex for sentiment analysis." Per source comments, user code is never logged and the telemetry is opt-out.
The leaked roadmap
The most strategically valuable piece of the leak.
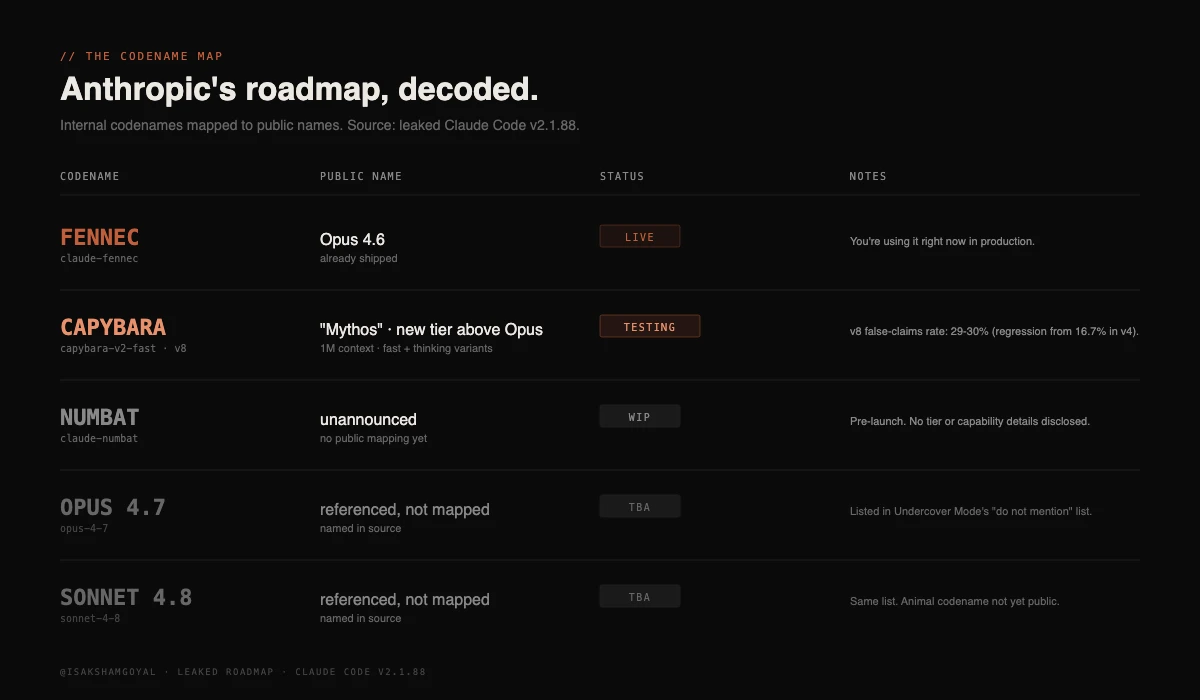 Leaked model codename roadmap
Leaked model codename roadmap
The Capybara line is the interesting one. The source references capybara-v2-fast with a 1M-token context window and separate "fast" and "thinking" tiers. This connects directly to the earlier Mythos leak: Capybara = Mythos = the new tier above Opus.
The leaked source also includes internal benchmark data Anthropic likely never intended to publish. Capybara v8's false-claims rate is logged at 29-30%, a regression from 16.7% on v4. Source comments describe an "assertiveness counterweight" built to prevent the model from making sweeping, destructive refactors as it gets more capable. The kind of internal calibration metric competitors will study closely.
Anthropic's response
The official statement positioned the leak as a packaging error and committed to tightening the build pipeline. No formal post-mortem.
Three things worth keeping straight:
- "Source available" is not "open source." Claude Code's license does not permit redistribution. The takedowns were legally enforceable.
- Model weights were never exposed. What leaked was the agent harness, the layer between the user and the underlying model. The model itself runs on Anthropic's servers.
- A separate
axiossupply-chain attack hit the same morning. Lockfiles should be checked foraxios@1.14.1,axios@0.30.4, orplain-crypto-js. Coincident, unrelated, but it amplified the security concern.
Why it matters
On packaging. Source maps are routine debugging artifacts. They are also a complete reverse-engineering kit when shipped to a public registry. Audit your .npmignore this week. The bar is one missing line.
On agent architecture. This is the most detailed publicly-visible reference for what a production-grade AI coding agent looks like. Multi-agent orchestration in a system prompt. Permission gating at six layers. Memory consolidation in idle time. Cryptographic client attestation. A category that previously lived mostly in research papers and vendor pitch decks.
On strategic leverage. The feature flag names alone may be more revealing than any line of code. KAIROS, ULTRAPLAN, the Capybara roadmap, anti-distillation. As one Hacker News commenter put it: you can refactor code in a week, but you cannot un-leak a roadmap.
For a company reportedly preparing for an IPO with $19B annualized revenue, 80% of it enterprise, the strategic damage likely exceeds the technical damage. The safety-first brand takes a hit no marketing campaign can patch.
Sources
- VentureBeat: Claude Code's source code appears to have leaked
- InfoQ: Anthropic Accidentally Exposes Claude Code Source via npm Source Map File
- Cybernews: Full source code for Anthropic's Claude Code leaks
- Zscaler ThreatLabz: Anthropic Claude Code Leak
- Layer5: The Claude Code Source Leak: 512,000 Lines
- Kilo Blog: Claude Code Source Leak: A Timeline
- ThePlanetTools: Claude Code Has a Secret Tamagotchi
- Sovereign Magazine: Anthropic Accidentally Leaked Claude Code Source Code
- decodethefuture.org: Opus 4.7, Sonnet 4.8, Capybara: Roadmap Decoded
- Original X post by @Fried_rice (Chaofan Shou)